An Nidps Can Tell You Whether an Attack Attempt on the Host Was Successful.
Acyber assault is any blazon of offensive action that targets computer information systems, infrastructures, computer networks or personal estimator devices, using various methods to steal, alter or destroy data or data systems.
Today I'll describe the 10 most mutual cyber attack types:
- Denial-of-service (DoS) and distributed denial-of-service (DDoS) attacks
- Human-in-the-middle (MitM) attack
- Phishing and spear phishing attacks
- Drive-by attack
- Password assail
- SQL injection attack
- Cross-site scripting (XSS) attack
- Eavesdropping attack
- Birthday assail
- Malware attack
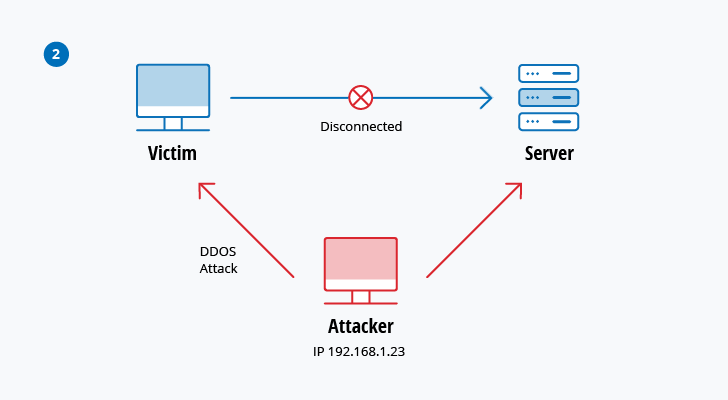
i. Denial-of-service (DoS) and distributed denial-of-service (DDoS) attacks
A denial-of-service attack overwhelms a system's resources so that it cannot answer to service requests. A DDoS attack is also an assail on organisation's resource, but information technology is launched from a big number of other host machines that are infected by malicious software controlled by the attacker.
Unlike attacks that are designed to enable the assaulter to gain or increment admission, deprival-of-service doesn't provide direct benefits for attackers. For some of them, it'southward enough to have the satisfaction of service denial. However, if the attacked resource belongs to a business concern competitor, then the benefit to the assailant may be real enough. Another purpose of a DoS assault tin can be to take a system offline and then that a dissimilar kind of assault can exist launched. One common example is session hijacking, which I'll depict afterwards.
There are different types of DoS and DDoS attacks; the most mutual are TCP SYN flood assail, teardrop attack, smurf attack, ping-of-decease set on and botnets.
TCP SYN flood attack
In this assail, an aggressor exploits the utilise of the buffer space during a Transmission Command Protocol (TCP) session initialization handshake. The attacker's device floods the target organisation's small in-procedure queue with connectedness requests, but it does not answer when the target system replies to those requests. This causes the target system to time out while waiting for the response from the assailant's device, which makes the system crash or become unusable when the connection queue fills upwards.
There are a few countermeasures to a TCP SYN flood assail:
- Place servers behind a firewall configured to finish entering SYN packets.
- Increment the size of the connectedness queue and subtract the timeout on open connections.
Teardrop set on
This attack causes the length and fragmentation first fields in sequential Internet Protocol (IP) packets to overlap one another on the attacked host; the attacked organization attempts to reconstruct packets during the process but fails. The target arrangement then becomes confused and crashes.
If users don't have patches to protect confronting this DoS attack, disable SMBv2 and cake ports 139 and 445.
Smurf assail
This assail involves using IP spoofing and the ICMP to saturate a target network with traffic. This assault method uses ICMP echo requests targeted at broadcast IP addresses. These ICMP requests originate from a spoofed "victim" address. For instance, if the intended victim address is x.0.0.10, the attacker would spoof an ICMP echo asking from x.0.0.10 to the circulate address 10.255.255.255. This request would go to all IPs in the range, with all the responses going dorsum to ten.0.0.10, overwhelming the network. This process is repeatable, and can be automated to generate huge amounts of network congestion.
To protect your devices from this set on, yous need to disable IP-directed broadcasts at the routers. This will prevent the ICMP echo broadcast asking at the network devices. Another option would be to configure the terminate systems to proceed them from responding to ICMP packets from broadcast addresses.
Ping of death attack
This type of set on uses IP packets to 'ping a target organization with an IP size over the maximum of 65,535 bytes. IP packets of this size are not immune, so aggressor fragments the IP bundle. Once the target arrangement reassembles the package, it can feel buffer overflows and other crashes.
Ping of decease attacks can be blocked by using a firewall that will cheque fragmented IP packets for maximum size.
Botnets
Botnets are the millions of systems infected with malware under hacker control in order to carry out DDoS attacks. These bots or zombie systems are used to comport out attacks against the target systems, frequently overwhelming the target system'southward bandwidth and processing capabilities. These DDoS attacks are difficult to trace considering botnets are located in differing geographic locations.
Botnets can exist mitigated past:
- RFC3704 filtering, which will deny traffic from spoofed addresses and help ensure that traffic is traceable to its correct source network. For case, RFC3704 filtering will drop packets from bogon list addresses.
- Black hole filtering, which drops undesirable traffic before it enters a protected network. When a DDoS attack is detected, the BGP (Edge Gateway Protocol) host should ship routing updates to ISP routers so that they road all traffic heading to victim servers to a null0 interface at the next hop.
2. Human-in-the-middle (MitM) attack
A MitM attack occurs when a hacker inserts itself between the communications of a client and a server. Here are some common types of human being-in-the-middle attacks:
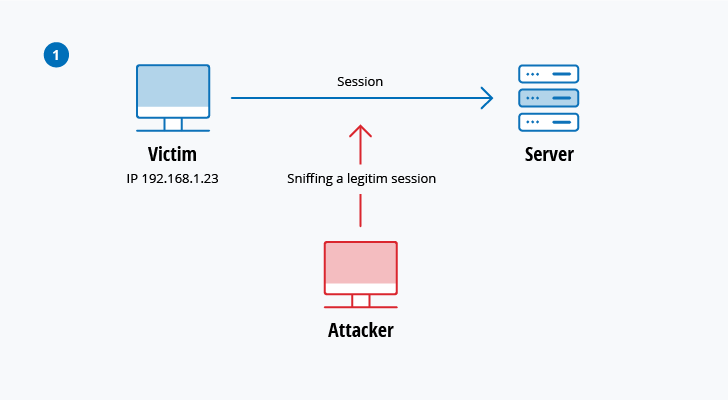
Session hijacking
In this type of MitM assail, an assailant hijacks a session between a trusted client and network server. The attacking computer substitutes its IP address for the trusted customer while the server continues the session, assertive information technology is communicating with the customer. For instance, the attack might unfold like this:
- A client connects to a server.
- The attacker'due south computer gains control of the client.
- The attacker's estimator disconnects the client from the server.
- The attacker's computer replaces the client'south IP address with its own IP address and
spoofs the client'south sequence numbers. - The assaulter's computer continues dialog with the server and the server believes it is nevertheless communicating with the customer.
IP Spoofing
IP spoofing is used by an attacker to convince a system that information technology is communicating with a known, trusted entity and provide the attacker with access to the organization. The attacker sends a packet with the IP source accost of a known, trusted host instead of its own IP source address to a target host. The target host might accept the packet and act upon information technology.
Replay
A replay set on occurs when an assailant intercepts and saves old messages and and then tries to send them afterward, impersonating ane of the participants. This type can be easily countered with session timestamps or nonce (a random number or a string that changes with time).
Currently, there is no single engineering science or configuration to prevent all MitM attacks. More often than not, encryption and digital certificates provide an effective safeguard against MitM attacks, assuring both the confidentiality and integrity of communications. But a man-in-the-middle attack can exist injected into the middle of communications in such a manner that encryption will non aid — for example, attacker "A" intercepts public cardinal of person "P" and substitute it with his own public key. And so, anyone wanting to send an encrypted message to P using P's public key is unknowingly using A'southward public key. Therefore, A tin can read the message intended for P and so send the message to P, encrypted in P's real public key, and P will never detect that the message was compromised. In add-on, A could besides modify the message earlier resending it to P. As y'all tin can see, P is using encryption and thinks that his information is protected but information technology is not, considering of the MitM set on.
Then, how tin you make certain that P'southward public key belongs to P and non to A? Document government and hash functions were created to solve this trouble. When person 2 (P2) wants to ship a message to P, and P wants to be sure that A will not read or change the message and that the bulletin actually came from P2, the following method must be used:
- P2 creates a symmetric cardinal and encrypts information technology with P's public key.
- P2 sends the encrypted symmetric central to P.
- P2 computes a hash part of the message and digitally signs it.
- P2 encrypts his message and the bulletin'due south signed hash using the symmetric key and sends the entire thing to P.
- P is able to receive the symmetric key from P2 because just he has the private primal to decrypt the encryption.
- P, and only P, can decrypt the symmetrically encrypted message and signed hash considering he has the symmetric primal.
- He is able to verify that the bulletin has not been contradistinct because he tin compute the hash of received message and compare it with digitally signed i.
- P is also able to testify to himself that P2 was the sender considering only P2 tin sign the hash and then that information technology is verified with P2 public key.
3. Phishing and spear phishing attacks
Phishing assault is the exercise of sending emails that appear to be from trusted sources with the goal of gaining personal information or influencing users to do something. It combines social technology and technical trickery. It could involve an zipper to an electronic mail that loads malware onto your computer. It could also exist a link to an illegitimate website that can trick you lot into downloading malware or handing over your personal information.
Spear phishing is a very targeted type of phishing activity. Attackers take the time to acquit inquiry into targets and create messages that are personal and relevant. Because of this, spear phishing can be very hard to place and fifty-fifty harder to defend against. One of the simplest ways that a hacker can comport a spear phishing attack is email spoofing, which is when the information in the "From" section of the email is falsified, making information technology announced as if it is coming from someone you know, such as your direction or your partner company. Another technique that scammers use to add brownie to their story is website cloning — they re-create legitimate websites to fool you into entering personally identifiable information (PII) or login credentials.
To reduce the risk of being phished, you can use these techniques:
- Critical thinking — Do non accept that an email is the real deal merely considering you're decorated or stressed or you have 150 other unread messages in your inbox. Stop for a minute and analyze the email.
- Hovering over the links — Move your mouse over the link, just do non click it! Just let your mouse cursor h over over the link and see where would really take you. Apply critical thinking to decipher the URL.
- Analyzing e-mail headers — Email headers ascertain how an email got to your address. The "Answer-to" and "Render-Path" parameters should lead to the same domain as is stated in the email.
- Sandboxing — You tin test email content in a sandbox surroundings, logging activity from opening the attachment or clicking the links inside the electronic mail.
four. Drive-by attack
Bulldoze-by download attacks are a mutual method of spreading malware. Hackers look for insecure websites and plant a malicious script into HTTP or PHP code on one of the pages. This script might install malware straight onto the computer of someone who visits the site, or information technology might re-direct the victim to a site controlled by the hackers. Drive-past downloads can happen when visiting a website or viewing an email message or a pop-upwards window. Dissimilar many other types of cyber security attacks, a drive-by doesn't rely on a user to do anything to actively enable the attack — you lot don't have to click a download button or open a malicious email attachment to become infected. A drive-by download tin can take advantage of an app, operating system or web browser that contains security flaws due to unsuccessful updates or lack of updates.
To protect yourself from drive-by attacks, you need to continue your browsers and operating systems up to date and avert websites that might comprise malicious lawmaking. Stick to the sites you lot usually utilise — although proceed in mind that fifty-fifty these sites can be hacked. Don't proceed as well many unnecessary programs and apps on your device. The more plug-ins yous have, the more than vulnerabilities at that place are that tin can be exploited past drive-by attacks.
5. Password assail
Because passwords are the almost usually used mechanism to authenticate users to an data system, obtaining passwords is a common and constructive assault arroyo. Admission to a person's password can be obtained past looking around the person'southward desk, ''sniffing'' the connection to the network to larn unencrypted passwords, using social engineering science, gaining admission to a password database or outright guessing. The concluding approach tin can exist done in either a random or systematic mode:
- Brute-force password guessing means using a random approach by trying dissimilar passwords and hoping that ane work Some logic can be applied by trying passwords related to the person's proper noun, job championship, hobbies or similar items.
- In a dictionary attack, a dictionary of common passwords is used to attempt to gain access to a user's figurer and network. I approach is to copy an encrypted file that contains the passwords, apply the same encryption to a dictionary of normally used passwords, and compare the results.
In society to protect yourself from dictionary or brute-strength attacks, you need to implement an account lockout policy that will lock the account after a few invalid password attempts. Yous can follow these business relationship lockout best practices in order to set it up correctly.
six. SQL injection set on
SQL injection has become a common issue with database-driven websites. It occurs when a malefactor executes a SQL query to the database via the input data from the customer to server. SQL commands are inserted into data-plane input (for instance, instead of the login or password) in order to run predefined SQL commands. A successful SQL injection exploit can read sensitive data from the database, modify (insert, update or delete) database data, execute administration operations (such as shutdown) on the database, recover the content of a given file, and, in some cases, issue commands to the operating system.
For example, a web course on a website might asking a user's account name and and so send information technology to the database in order to pull up the associated account information using dynamic SQL like this:
"SELECT * FROM users WHERE account = '" + userProvidedAccountNumber +"';"
While this works for users who are properly entering their business relationship number, information technology leaves a hole for attackers. For example, if someone decided to provide an account number of "' or 'i' = '1'", that would consequence in a query string of:
"SELECT * FROM users WHERE account = '' or '1' = 'ane';"
Considering '1' = '1' always evaluates to TRUE, the database will return the data for all users instead of just a single user.
The vulnerability to this type of cyber security assault depends on the fact that SQL makes no real distinction between the command and data planes. Therefore, SQL injections piece of work mostly if a website uses dynamic SQL. Additionally, SQL injection is very common with PHP and ASP applications due to the prevalence of older functional interfaces. J2EE and ASP.NET applications are less likely to have hands exploited SQL injections because of the nature of the programmatic interfaces available.
In society to protect yourself from a SQL injection attacks, apply least0privilege model of permissions in your databases. Stick to stored procedures (make sure that these procedures don't include any dynamic SQL) and prepared statements (parameterized queries). The code that is executed against the database must be strong enough to forbid injection attacks. In addition, validate input information confronting a white listing at the awarding level.
7. Cross-site scripting (XSS) assail
XSS attacks utilize third-party spider web resources to run scripts in the victim's web browser or scriptable application. Specifically, the aggressor injects a payload with malicious JavaScript into a website's database. When the victim requests a page from the website, the website transmits the page, with the attacker's payload as part of the HTML body, to the victim'southward browser, which executes the malicious script. For example, information technology might send the victim's cookie to the attacker's server, and the attacker can extract information technology and employ it for session hijacking. The most dangerous consequences occur when XSS is used to exploit additional vulnerabilities. These vulnerabilities can enable an attacker to non only steal cookies, just also log key strokes, capture screenshots, discover and collect network data, and remotely access and control the victim's machine.
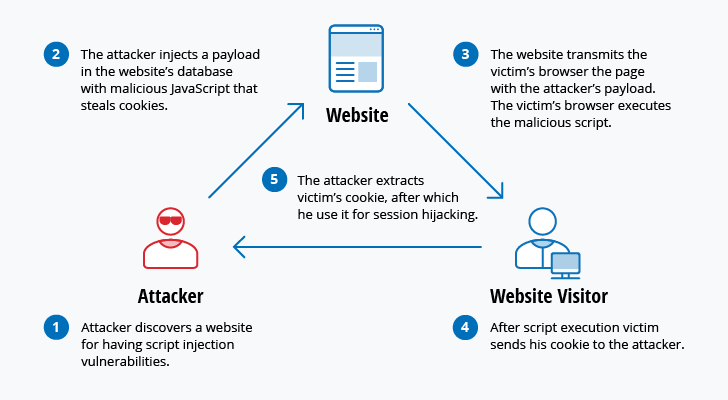
While XSS can be taken advantage of within VBScript, ActiveX and Flash, the most widely abused is JavaScript — primarily because JavaScript is supported widely on the web.
To defend against XSS attacks, developers can sanitize data input by users in an HTTP asking before reflecting information technology back. Brand sure all information is validated, filtered or escaped before echoing anything back to the user, such as the values of query parameters during searches. Convert special characters such as ?, &, /, <, > and spaces to their respective HTML or URL encoded equivalents. Give users the option to disable client-side scripts.
eight. Eavesdropping attack
Eavesdropping attacks occur through the interception of network traffic. By eavesdropping, an attacker can obtain passwords, credit card numbers and other confidential information that a user might be sending over the network. Eavesdropping can be passive or active:
- Passive eavesdropping — A hacker detects the data by listening to the message manual in the network.
- Active eavesdropping — A hacker actively grabs the information by disguising himself as friendly unit and by sending queries to transmitters. This is called probing, scanning or tampering.
Detecting passive eavesdropping attacks is often more important than spotting active ones, since agile attacks requires the attacker to gain noesis of the friendly units by conducting passive eavesdropping before.
Information encryption is the best countermeasure for eavesdropping.
ix. Altogether attack
Altogether attacks are made confronting hash algorithms that are used to verify the integrity of a message, software or digital signature. A message processed by a hash function produces a message digest (MD) of fixed length, independent of the length of the input message; this Physician uniquely characterizes the message. The altogether set on refers to the probability of finding ii random messages that generate the aforementioned Medico when candy by a hash function. If an attacker calculates same Doctor for his message equally the user has, he tin can safely replace the user'southward bulletin with his, and the receiver volition not be able to detect the replacement fifty-fifty if he compares MDs.
10. Malware attack
Malicious software can be described equally unwanted software that is installed in your system without your consent. It can adhere itself to legitimate lawmaking and propagate; it can lurk in useful applications or replicate itself across the Net. Here are some of the about common types of malware:
- Macro viruses — These viruses infect applications such as Microsoft Give-and-take or Excel. Macro viruses attach to an application'due south initialization sequence. When the application is opened, the virus executes instructions earlier transferring control to the application. The virus replicates itself and attaches to other code in the computer system.
- File infectors — File infector viruses usually attach themselves to executable lawmaking, such equally .exe files. The virus is installed when the code is loaded. Some other version of a file infector assembly itself with a file by creating a virus file with the same proper noun, but an .exe extension. Therefore, when the file is opened, the virus code will execute.
- System or boot-tape infectors — A kicking-record virus attaches to the chief kick record on difficult disks. When the organization is started, it volition look at the boot sector and load the virus into memory, where information technology can propagate to other disks and computers.
- Polymorphic viruses — These viruses muffle themselves through varying cycles of encryption and decryption. The encrypted virus and an associated mutation engine are initially decrypted by a decryption plan. The virus proceeds to infect an surface area of code. The mutation engine and so develops a new decryption routine and the virus encrypts the mutation engine and a re-create of the virus with an algorithm corresponding to the new decryption routine. The encrypted parcel of mutation engine and virus is attached to new code, and the process repeats. Such viruses are difficult to detect but have a high level of entropy considering of the many modifications of their source code. Anti-virus software or complimentary tools like Process Hacker tin use this feature to detect them.
- Stealth viruses — Stealth viruses have over system functions to muffle themselves. They practice this by compromising malware detection software then that the software will report an infected area as being uninfected. These viruses conceal whatever increase in the size of an infected file or changes to the file'south date and time of last modification.
- Trojans — A Trojan or a Trojan horse is a program that hides in a useful program and usually has a malicious role. A major difference between viruses and Trojans is that Trojans do not cocky-replicate. In addition to launching attacks on a organisation, a Trojan can establish a dorsum door that can be exploited past attackers. For example, a Trojan can be programmed to open up a high-numbered port so the hacker can use it to listen and so perform an set on.
- Logic bombs — A logic flop is a type of malicious software that is appended to an application and is triggered by a specific occurrence, such equally a logical condition or a specific date and time.
- Worms — Worms differ from viruses in that they do non attach to a host file, but are self-contained programs that propagate across networks and computers. Worms are commonly spread through e-mail attachments; opening the zipper activates the worm programme. A typical worm exploit involves the worm sending a copy of itself to every contact in an infected calculator's electronic mail address In improver to conducting malicious activities, a worm spreading across the net and overloading email servers tin can result in denial-of-service attacks against nodes on the network.
- Droppers — A dropper is a programme used to install viruses on computers. In many instances, the dropper is not infected with malicious code and, therefore might non exist detected by virus-scanning software. A dropper can also connect to the internet and download updates to virus software that is resident on a compromised system.
- Ransomware — Ransomware is a type of malware that blocks access to the victim's information and threatens to publish or delete it unless a ransom is paid. While some simple reckoner ransomware tin can lock the system in a fashion that is non difficult for a knowledgeable person to reverse, more advanced malware uses a technique called cryptoviral extortion, which encrypts the victim's files in a manner that makes them well-nigh impossible to recover without the decryption key.
- Adware — Adware is a software application used by companies for marketing purposes; advertising banners are displayed while whatever program is running. Adware can exist automatically downloaded to your system while browsing any website and can be viewed through pop-up windows or through a bar that appears on the computer screen automatically.
- Spyware — Spyware is a blazon of plan that is installed to collect information about users, their computers or their browsing habits. It tracks everything you lot do without your noesis and sends the data to a remote user. It also can download and install other malicious programs from the internet. Spyware works like adware only is usually a split program that is installed unknowingly when yous install another freeware application.
Conclusion
Mounting a practiced defense force requires understanding the offense. This article has reviewed the 10 most common cyber-security attacks that hackers apply to disrupt and compromise information systems. As y'all can meet, attackers have many options, such as DDoS assaults, malware infection, man-in-the-middle interception, and animal-force countersign guessing, to trying to gain unauthorized access to critical infrastructures and sensitive data.
Measures to mitigate these threats vary, but security basics stay the aforementioned: Keep your systems and anti-virus databases upward to appointment, train your employees, configure your firewall to whitelist merely the specific ports and hosts you lot need, proceed your passwords strong, employ a least-privilege model in your It environment, make regular backups, and continuously inspect your It systems for suspicious activity.

Source: https://blog.netwrix.com/2018/05/15/top-10-most-common-types-of-cyber-attacks/
0 Response to "An Nidps Can Tell You Whether an Attack Attempt on the Host Was Successful."
Post a Comment